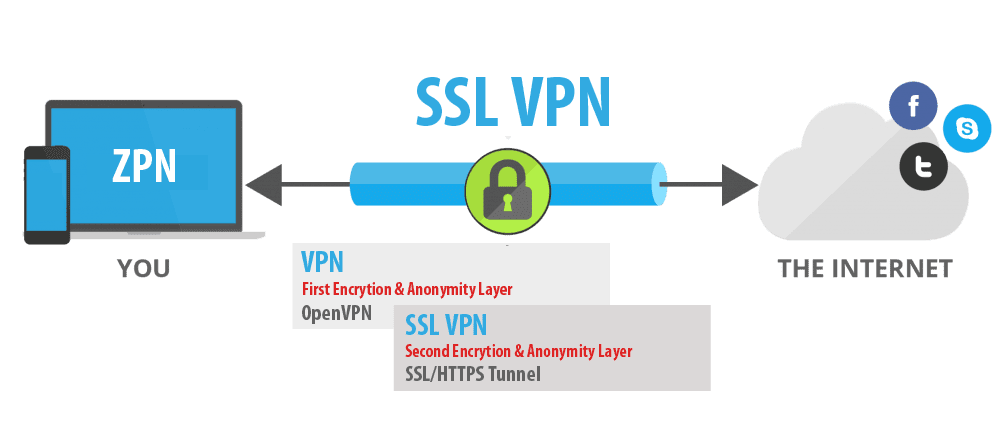
Well, you must be aware of the fact that a VPN is the software tool that guarantees you private browsing on the internet, right? Because of a VPN, your online activity and data transmitted between the different servers you access to make you anonymous.
Cybercriminals are always on the lookout to cash in on personal data such as passwords and credit card details. You definitely want to keep yourself invisible from these malicious activities online.
VPNs work with different security protocols. These protocols such as the Security Socket tunneling Protocol uses an SSL certificate for authentication. BestVPN.com has a list of some of the best VPN products in the market with their specifications to help you select the best VPN for your security needs.
We also have the SSN VPN products, commonly known as SSL VPNs. SSL VPNs primarily function to secure network communication and connections.
Let’s have a deep dive into all the fuss about SSL VPNs and get to know some of its best products in the market.
SSL VPNs are like your watchmen online. They encrypt a network’s activity thereby protecting a communication’s privacy and decency between individual devices and a VPN channel.
Individual devices for that matter include laptops, mobile devices, servers, and desktops. However, there is a little bit of a twist into how these SSL VPNs function today.
They now focus on specific targets to secure remote access for devices belonging to individual clients alone. They no longer work with servers and other network devices.
Technically, it means a single SSL VPN server serving as a gateway to SSL VPN clientele wanting to get access to a corporate network.
The logic behind the use of an SSL VPN Product
In a network communication, there are several unwarranted parties who may want to eavesdrop on the details of your communication. This, they do with the intention of extracting crucial information from your data.
In most cases, eavesdropping targets client devices that get connected through external networks and their network traffic is being channeled through the internet. Also, wireless access points that aren’t secured are a potential target by eavesdroppers.
You also want your network communication not manipulated or interrupted by attackers who could easily alter your data. In most cases, this occurs without your knowledge
Nowadays, SSL VPNs are rarely sold separately as stand-alone products. Most vendors have resorted to integrating SSL VPN features into Unified threat management (UTM), Next Generation Firewalls (NGFS) systems and several other network security systems.
Other security benefits that come with an SSL VPN include:
- You get to have a centralized access control for a wide range of corporate resources.
- You have an additional layer of authentication for security purposes that also involves centralized auditing and monitoring.
- Routine performance of safety health checks to clients using organizational resources.
An SSL VPN product could be deployed as a virtual or standalone appliance or come bundled together. Most organizations may be lost on the criteria they need to use in evaluating the best SSL VPN service for their IT environment and network security needs.
With many vendors of the SSL VPN technology, you could be left spoilt for choice on what SSL VPN best suits your organization needs. However, here is a list of some of the best SSL products in the market.
Check Point Mobile Access Software Blade
This type of SSL VPN product suits a broad range of Check Point gadgets. Desktops, laptops and mobile devices running on Android or iOS can make good use of it.
With this SSL VPN product, you got the advantage of several authentication products and specification like the single sign-on. Single sign-on makes it possible for organizations to enforce enterprise security policies on the devices of their clients.
Barracuda

Barracuda is a versatile SSL VPN that can support up to 100 concurrent users. This is made possible by the virtual appliance systems and the wide range of hardware it contains.
This SSL VPN is worth using as it supports most operating systems. It also works well with different browser versions. Most Barracuda appliance models that operate beyond 25 concurrent users come with a wide range of benefits.
You are guaranteed network access control. This ensures your device is kept safe under their models that support security policies. You are also assured of logging and enterprise authentication features.
Cisco IOS

This SSL VPN comes as software for a number of Cisco router models. Several browser plug-ins such as Active X and Java make use of it. If you operate a small or medium organization that houses up to 200 users, Cisco IOS works well for you.
It is also available for several operating systems that run on Windows and desktop. However, it is yet to be popular with the operating system of a mobile device.
Like the Barracuda SSL VPN, Cisco IOS enables you to access network controlling features and enterprise authentication incorporation.
OpenVPN access server

This SSL VPN provides a secure remote access for enterprises. It carries internet traffic through an encrypted tunnel. This means your internet data is protected from eavesdroppers and prying eyes.
It’s traditional software that has cloud and virtualization-based products that enable the implementation of SSL VPN functionalities. It virtually supports almost every network including Mac OS, X, Linux and Mobile operating systems.
Juniper Networks SA series
The Juniper Networks contain virtual appliance options that can work in organizations that have a maximum of 100 concurrent users. It has plug-in options that are Java-based allowing it to be accessible from any Web browser or operating system. It comes with common authentication features and strong network access control abilities.
Conclusion
SSL VPN types work to protect your internet traffic from any prying eyes on the internet. Most protect your data using an encryption tunnel.
The choice of the SSL VPN type to use lies squarely on the shoulders of companies and organizations. While the SSL VPNs listed are not bad in any way, companies need to choose an SSL VPN type that best work for their organizational needs.